Built to help you achieve compliance with:
Checklists and dashboards don't pass audits.
Defensible evidence does.
CyberAudit is audit-defensible evidence and verification software. Built for compliance leaders, CISOs, internal audit, and regulated organizations—and for the external auditors and procurement reviewers who assess them.
Verification Over Inference
Controls verified and recorded, not assumed
Scale How You Need
From one endpoint to thousands
Compliance Frameworks
SOC 2, ISO, NIST, CMMC, HIPAA & more
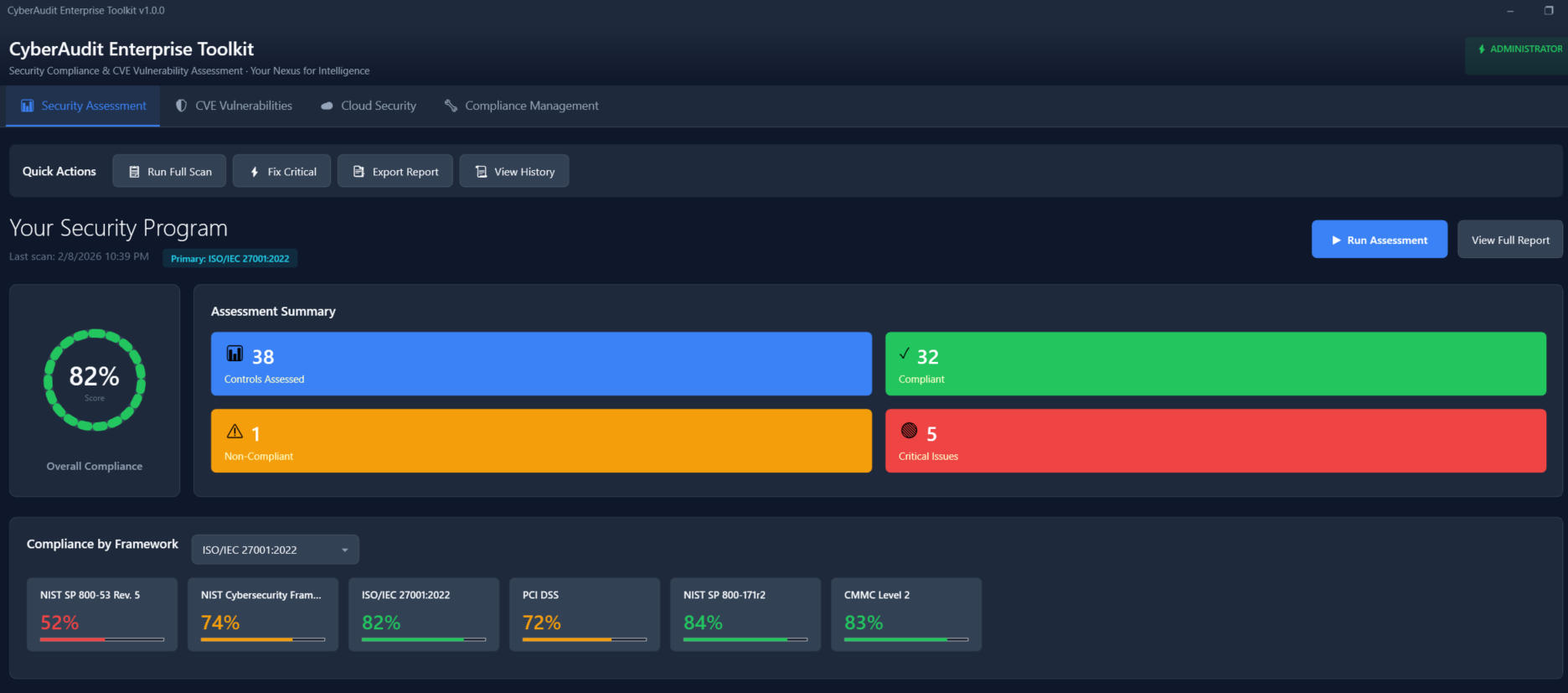
Your Complete Security Program at a Glance
Real-time visibility into your compliance posture
Trusted by compliance teams at
What Compliance Leaders Say
Join hundreds of organizations that trust CyberAudit
"CyberAudit has transformed how we approach compliance. The evidence quality is exactly what our auditors need."
Sarah Johnson
CISO, Defense Contractor
"We passed our CMMC Level 2 audit on the first try. The auditor was impressed with our documentation."
Michael Chen
VP Compliance, Aerospace
"Finally, a compliance tool that auditors actually respect. Our last three audits were smoother than ever."
Emily Rodriguez
Director, Internal Audit
What CyberAudit guarantees
We state guarantees and constraints, not a feature list. The following hold for the platform:
Verification over inference
Controls are verified and recorded. We do not infer satisfaction from partial data.
Preserved exceptions
Failures and gaps are recorded and retained. They are not hidden or overwritten.
Repeatable outcomes
The same process yields the same class of outputs: evidence, audit history, and control-to-evidence mapping that can be reproduced for review.
Who CyberAudit is built for
Primary: compliance leaders, CISOs, internal audit, and regulated organizations that need defensible evidence and verification—not another dashboard. Secondary: external auditors and procurement reviewers who need to assess evidence quality and traceability.
For auditors: Built for auditors
Ready to transform your compliance program?
Evidence flow, controls, and what reviewers receive—without the gloss.